In today’s increasingly interconnected world, cyber threats are becoming more sophisticated and widespread. As a result, it is more important than ever for individuals and organizations to take proactive measures to protect themselves from potential harm.
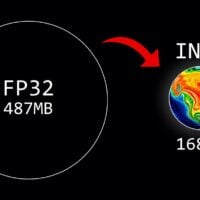
What Does Quantization Mean and How Does It Shrink AI Models?
Quantization is a technique used to reduce the size of machine learning models while maintaining accuracy. This can lead to faster deployment times, lower memory usage, and reduced bandwidth requirements when deploying these models on edge devices or in other resource-constrained environments.
Social Engineering Attacks: Evolving Threats and Proactive Measures
Social engineering attacks have been a persistent threat in the cybersecurity landscape, preying on human vulnerabilities rather than technical weaknesses. As technology continues to advance, so too do these tactics, becoming more sophisticated and convincing.
The Latest Trends in Artificial Intelligence
Artificial Intelligence (AI) is a rapidly evolving field that has seen significant advancements in recent years. As AI technology continues to develop and mature, new trends are emerging that are shaping the future of this exciting industry. In this article, we will discuss some of the latest trends in AI that are currently capturing the attention of researchers, developers, and users alike.
The Updated NIST Cybersecurity Framework 2.0
The National Institute of Standards and Technology (NIST) has recently updated its Cybersecurity Framework for 2024. This is an important development that businesses need to take into account when developing their own cybersecurity best practices. In this article, we will discuss the changes made by NIST and how businesses can use these updates as a reference point for their own cybersecurity frameworks.