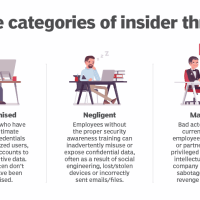
In the realm of cybersecurity, the risk of insider threats, encompassing both compromised and negligent employees as well as those who intentionally go rogue, is a critical and often overlooked aspect.
The Virginia Consumer Data Protection Act and You
In March 2021, the Commonwealth of Virginia enacted the Virginia Consumer Data Protection Act (VCDPA), a significant move towards enhancing the data privacy rights of Virginia residents. This act, effective from January 1, 2023, is the state’s principal consumer data protection law, and it’s crucial for businesses worldwide dealing with clients in Virginia to understand its implications.
Our 2024 Outlook: Trends, Threats and Predictions
In the dynamic world of digital security, 2023 was a landmark year that witnessed a significant surge in the scale and impact of cybersecurity breaches. This article aims to dissect these developments and project the implications for 2024, emphasizing the need for enhanced cybersecurity preparedness and resilience.
The Growing Danger of Ransomware
The evolution of ransomware threats in 2023 has marked a significant escalation in their sophistication and impact. The 2023 State of Ransomware Report revealed that ransomware attacks have reached an all-time high, with the United States bearing a substantial 43% of these global attacks. Notably, France saw its ransomware attacks nearly double in just five months. The year 2023 saw a continuation of the upward trend in ransomware activities that began in 2022, with high-profile attacks targeting major corporations like Toyota and Boeing, exploiting vulnerabilities like Citrix Bleed (CVE-2023-4966).
Cybersecurity Measures for Small Businesses to Consider
In the digital age, small businesses must navigate a landscape filled with cyber threats. While large corporations have extensive resources to mitigate cyber risks, small businesses often operate with more limited budgets and IT expertise. However, cybersecurity is not a luxury—it’s a necessity.